OS Unix obtain opens a world of highly effective and customizable working programs. This complete information delves into the intricacies of buying, putting in, and utilizing Unix-like programs. We’ll discover the various panorama of distributions, detailing obtain processes, system necessities, and essential set up steps. Put together to embark on a journey of discovery as we navigate the world of Unix-like working programs.
From the preliminary obtain to the ultimate configuration, this useful resource supplies a transparent and concise roadmap. Uncover the advantages of various distributions, and perceive the important safety concerns that accompany this highly effective know-how. Achieve a deeper understanding of the various decisions accessible and how you can choose the perfect Unix-like system to your wants. Unlock the potential of those superior working programs.
Totally different Unix Distributions

Unix, a strong working system, has spawned a various household of distributions, every tailor-made for particular wants and preferences. These variations, whereas sharing a standard lineage, supply distinct options and functionalities, making them interesting to a variety of customers and use circumstances. This exploration delves into the important thing traits, distinctions, and purposes of standard Unix-like programs.
Well-liked Unix-like Working Techniques
A big selection of working programs, deeply rooted within the Unix philosophy, have emerged. These embody Linux distributions, BSD variants, and different Unix-inspired programs. Every possesses distinctive strengths, catering to totally different person necessities and improvement objectives.
- Linux Distributions: An unlimited assortment of working programs based mostly on the Linux kernel. This kernel supplies the core functionalities, whereas distributions add purposes, utilities, and desktop environments. Distributions like Ubuntu, Fedora, Debian, and CentOS are examples of standard Linux programs.
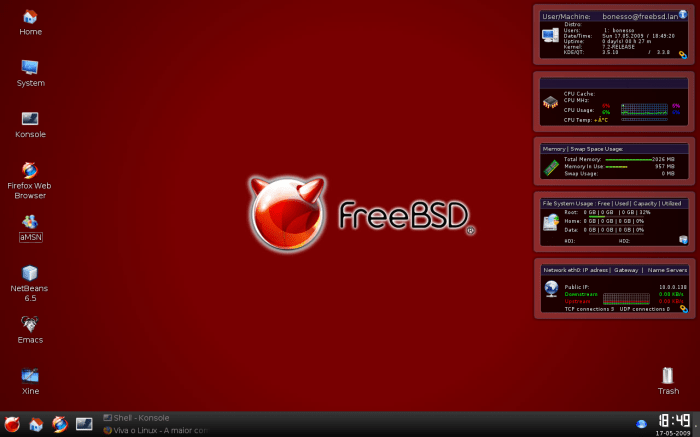
- BSD (Berkeley Software program Distribution) Variants: Derived from the unique Unix, BSD distributions are recognized for his or her safety, stability, and deal with networking. FreeBSD, OpenBSD, and NetBSD are notable examples, every with its distinctive design and have set.
- Different Unix-inspired Techniques: A various group of working programs, together with Solaris (now largely defunct), macOS (a proprietary system with Unix underpinnings), and others, typically emphasizing particular niches, like high-performance computing or embedded programs.
Key Variations Between Working Techniques
The core distinction lies within the kernel and the accompanying software program packages. Linux distributions, as an example, supply a wider vary of decisions for desktop environments, purposes, and customization choices. BSD programs typically prioritize safety and networking options. These distinctions affect their respective use circumstances.
Variations and Releases
Every working system undergoes common updates and releases, including new options, enhancing stability, and patching safety vulnerabilities. These variations are essential for sustaining performance and addressing potential points. Monitoring these releases ensures customers have the most recent enhancements and bug fixes. The frequency and nature of releases range amongst distributions.
Typical Use Circumstances
The meant utilization of every system is numerous. Linux distributions are ceaselessly utilized in servers, embedded programs, and desktop environments. BSD programs are prevalent in networking, security-sensitive purposes, and high-performance computing.
Licensing Fashions, Os unix obtain
Licensing fashions range significantly. Most Linux distributions are based mostly on the GNU Normal Public License (GPL), selling open-source improvement and neighborhood participation. BSD distributions typically use the BSD license, which permits for flexibility in utilization and industrial improvement.
Comparability Desk of Unix Distributions
| Identify | Origin | License | Typical Use Circumstances |
|---|---|---|---|
| Ubuntu | Canonical | GPL | Desktop environments, servers, cloud computing |
| Fedora | Pink Hat | GPL | Improvement, testing, servers, desktop |
| Debian | Debian Venture | GPL | Servers, desktops, embedded programs |
| FreeBSD | College of California, Berkeley | BSD | Servers, networking, security-focused purposes |
| OpenBSD | OpenBSD Venture | BSD | Safety-critical purposes, networking |
Obtain Strategies and Processes
Getting your arms on a Unix distribution is like selecting a brand new software for a posh undertaking. Realizing how you can obtain it correctly is essential, whether or not you are a seasoned developer or a curious newbie. Totally different strategies supply numerous benefits, and understanding their nuances will assist you to make the suitable selection to your wants.
Direct Obtain
Direct downloads are simple. You discover the official obtain web page to your desired distribution, find the suitable package deal, and provoke the obtain. This technique is mostly dependable if you happen to’re conversant in the distribution’s web site and its obtain construction. It is also a very good possibility for smaller distributions or particular recordsdata. Crucially, at all times scrutinize the obtain hyperlink to make sure its legitimacy.
Utilizing a Package deal Supervisor
Package deal managers are highly effective instruments for managing software program, together with working programs. For a lot of distributions, a package deal supervisor like apt (for Debian-based programs) or yum (for Pink Hat-based programs) supplies a structured strategy to downloading and putting in. This technique streamlines the method and presents automated updates and dependencies, which is extremely really helpful for constant programs. It is important to make sure the package deal supervisor is configured appropriately and up to date to the most recent model.
Cloud Providers
Cloud providers, similar to Amazon Internet Providers (AWS) or Google Cloud Platform (GCP), typically supply pre-configured pictures of Unix distributions. This can be a handy technique for deploying programs shortly. This technique is right for conditions requiring speedy deployment or when entry to a neighborhood machine is restricted. Bear in mind that these strategies may contain prices and particular utilization phrases.
Examples of Obtain Hyperlinks
Listed here are some examples of obtain hyperlinks for widespread distributions:
- Ubuntu: [Insert example link here for Ubuntu]
- Debian: [Insert example link here for Debian]
- Fedora: [Insert example link here for Fedora]
Word: These examples are placeholders. At all times confirm the hyperlinks with the official distribution web site.
Verifying the Supply of the Obtain
Belief is paramount. Make sure the obtain hyperlink originates from the official distribution web site. Phishing makes an attempt and malicious actors exist. Search for HTTPS, a safe connection, to confirm the positioning’s authenticity. Confirm the positioning’s area and certificates to make sure you’re on the real platform.
Potential Dangers of Unofficial Sources
Downloading from unofficial sources introduces important dangers. These sources may include malware or corrupted recordsdata. Unofficial downloads typically lack essential safety updates, leaving programs weak to exploitation. At all times prioritize official channels to make sure your system’s security.
Checking the Integrity of a Downloaded File
Checking the integrity of a downloaded file is a vital step to stop malicious modifications. Official distributions typically present checksums (MD5, SHA-256) that can be utilized to validate the downloaded file. Evaluate the checksum of the downloaded file with the one offered on the official web site to confirm its authenticity.
Obtain Strategies Comparability
| Obtain Technique | Execs | Cons |
|---|---|---|
| Direct Obtain | Easy, simple | Requires handbook verification, potential for errors |
| Package deal Supervisor | Automated, safe, up to date | Requires appropriate configuration, potential dependency points |
| Cloud Service | Quick deployment, flexibility | Value, restricted management, potential service outages |
System Necessities and Compatibility

Embarking on the Unix-like journey requires understanding the terrain. Totally different distributions, from light-weight to powerhouse, have various wants. This part delves into the essential points of {hardware} and software program compatibility, guaranteeing a easy journey.Navigating the world of Unix-like programs includes understanding the precise necessities for every working system. Compatibility is not nearly {hardware}; it additionally encompasses the software program ecosystem.
A well-matched system permits for a seamless and pleasing expertise, avoiding irritating glitches and compatibility points.
Minimal System Necessities
To make sure a constructive expertise, understanding the minimal necessities for various Unix-like distributions is important. These necessities are the bedrock of profitable installations.
- Totally different distributions cater to varied wants and efficiency expectations. Light-weight distributions typically require much less highly effective {hardware}, whereas extra feature-rich distributions demand extra sturdy configurations.
- Processor necessities range considerably, starting from older dual-core processors to trendy multi-core architectures. The complexity of the software program determines the mandatory processor pace.
- RAM necessities additionally play an important position. Fashionable distributions with in depth graphical interfaces and demanding purposes demand larger RAM capability.
- Space for storing is important for storing the working system recordsdata, purposes, and person information. Adequate cupboard space is significant to make sure a easy and uninterrupted person expertise.
{Hardware} and Software program Compatibility
Compatibility is extra than simply assembly minimal necessities; it is a couple of harmonious relationship between {hardware} and software program. A well-balanced setup avoids potential points.
- {Hardware} compatibility is essential for easy operation. Drivers and firmware have to be suitable with the {hardware} elements.
- Software program compatibility includes guaranteeing the purposes and utilities work seamlessly with the working system.
- Kernel compatibility is a important factor. The kernel, the core of the working system, should work together flawlessly with the {hardware} to handle system sources effectively.
Instance {Hardware} Configurations
Contemplate these instance configurations for various Unix-like programs, showcasing the adaptability and energy of the know-how.
- A fundamental configuration for a light-weight distribution may embody a dual-core processor, 4GB of RAM, and 32GB of storage.
- A extra demanding configuration for a desktop setting might contain a quad-core processor, 8GB of RAM, and 128GB of storage.
- A server configuration would demand a multi-core processor, important RAM (typically measured in tens or a whole bunch of GB), and a high-capacity storage system.
Checking System Compatibility
Verifying system compatibility earlier than set up is essential to keep away from sudden points. Thorough checks guarantee a constructive set up course of.
- Seek the advice of the precise distribution’s web site for detailed system necessities. These sources are often available.
- Make the most of on-line compatibility checkers. Many instruments exist to check your {hardware} in opposition to the necessities of a selected distribution.
- Fastidiously evaluate the distribution’s documentation to grasp the nuances of {hardware} and software program compatibility. This may assist you to make knowledgeable selections.
Set up Procedures
Set up procedures range amongst Unix-like distributions. An in depth understanding of the method is essential.
- Set up strategies can vary from easy USB drives to extra advanced server deployments. Totally different strategies cater to varied wants and environments.
- Set up processes could contain partitioning arduous drives, creating boot loaders, and configuring system settings. The precise steps depend upon the distribution and desired setup.
- Detailed directions for set up procedures are often accessible on-line. Discuss with the official documentation for correct and up-to-date data.
Comparability of Set up Processes
Evaluating set up processes throughout numerous distributions helps perceive their strengths and weaknesses. Totally different distributions supply distinctive benefits.
- Totally different distributions use totally different package deal managers and installer instruments. Every strategy has its personal strengths and weaknesses.
- Some distributions supply graphical installers, whereas others depend on command-line instruments. The chosen strategy impacts the person expertise.
- Set up procedures for server deployments typically differ from these for desktop environments. The necessities and steps depend upon the meant use.
System Necessities Desk
This desk supplies a fast reference for the minimal system necessities throughout totally different Unix-like working programs.
| Working System | Processor Necessities | RAM | Storage Area | Instance {Hardware} |
|---|---|---|---|---|
| Linux Mint | Twin-core processor | 4 GB | 32 GB | Desktop PC |
| Ubuntu | Twin-core processor | 4 GB | 32 GB | Laptop computer |
| macOS | Intel processor | 8 GB | 64 GB | Desktop Mac |
Set up Procedures
Embarking on a Unix-like journey typically begins with an important step: set up. This course of, whereas seemingly simple, includes cautious consideration of a number of components to make sure a easy and profitable transition. From deciding on the suitable set up media to configuring your system post-installation, each side performs a important position in your expertise.Selecting the best distribution and set up technique is akin to deciding on the right software for a selected job.
A well-suited distribution, alongside a correct set up technique, can considerably influence your system’s efficiency, safety, and general usability. This part will information you thru the intricacies of set up, empowering you to confidently navigate the method and embrace the ability of Unix-like programs.
Choosing the Proper Set up Media
The set up media you select instantly impacts the set up course of. Utilizing the proper media ensures a seamless transition, stopping potential errors or compatibility points. This consists of understanding the variations between bootable USB drives, DVDs, and even community installations.Totally different media varieties have totally different benefits. For example, USB drives are transportable and ideally suited for experimenting with numerous distributions. DVDs, whereas barely much less widespread now, supply the benefit of enormous cupboard space for advanced installations.
Community installations permit for the distribution to be downloaded and put in instantly onto your system. The selection relies on your particular wants and sources.
Totally different Set up Choices
Understanding the assorted set up choices is essential to optimizing your system to your wants. A full set up usually supplies a whole setting, whereas a minimal set up presents a streamlined expertise. The selection between a full and minimal set up relies in your meant utilization.
- Full Set up: A full set up is the excellent strategy, offering all of the important elements and utilities of the chosen distribution. This feature is right for these looking for a whole and ready-to-use setting. This set up possibility is like establishing a completely furnished house; every thing you want is available.
- Minimal Set up: A minimal set up prioritizes the naked requirements, offering solely the core elements required for system operation. That is appropriate for customers who want a fundamental platform for particular duties or who need to tailor their system additional. This set up strategy is like beginning with a clean house; you may have the muse and might customise it as you see match.
Getting ready the System for Set up
Thorough preparation earlier than set up minimizes potential points and maximizes effectivity. This includes guaranteeing the system is correctly backed up, having the mandatory sources, and understanding the distribution’s particular stipulations.
- Backup: Backing up your current system information is essential. This protects your beneficial recordsdata in case of unexpected errors throughout the set up course of. Consider this as safeguarding your necessary belongings earlier than beginning a renovation undertaking.
- Assets: Guarantee your system has ample cupboard space, RAM, and processing energy. The necessities for a easy set up will range based mostly on the chosen distribution. Contemplate this as guaranteeing you may have the suitable instruments and supplies earlier than enterprise a development undertaking.
- Stipulations: The precise distribution you select might need stipulations for a profitable set up. These might contain having a sure model of a selected software or program. That is like guaranteeing you may have the mandatory permits earlier than beginning a development undertaking.
Put up-Set up Configuration Duties
Put up-installation configuration duties are important for optimizing your newly put in system. This includes establishing person accounts, configuring community settings, putting in essential drivers, and customizing the system’s look and performance.
- Consumer Accounts: Organising person accounts lets you handle permissions and entry to system sources successfully.
- Community Settings: Configuring community settings permits your system to connect with the web and different units seamlessly.
- Drivers: Putting in essential drivers is essential to your system to acknowledge and make the most of {hardware} elements correctly.
- Customization: Tailoring the system’s look and performance to your preferences ensures a snug and environment friendly person expertise.
Step-by-Step Set up Process (Instance: Ubuntu)
This instance Artikels the set up of Ubuntu.
- Boot from the Ubuntu set up media.
- Select your language and keyboard structure.
- Choose the set up kind (full or minimal).
- Select the partition scheme.
- Enter the specified person particulars.
- Set up the chosen elements.
- Configure community settings and different essential choices.
- Reboot the system.
Set up Choices Desk
| Set up Possibility | Description | Advantages |
|---|---|---|
| Full Set up | Contains all essential packages and utilities | Prepared-to-use system, complete performance |
| Minimal Set up | Contains solely important packages | Light-weight system, customizable setting |
Frequent Points and Troubleshooting
Navigating the digital panorama of Unix-like programs can generally really feel like a treasure hunt. Easy crusing is not at all times assured, and occasional hiccups are inevitable. This part arms you with the instruments and information to beat widespread obstacles encountered throughout obtain and set up, guaranteeing a seamless transition to your new system.
Figuring out Frequent Obtain Issues
Obtain failures are sometimes rooted in community instability or server points. Inconsistent web connectivity, firewalls, or proxy settings can disrupt the obtain course of. Confirm your community connection, examine firewall configurations, and regulate proxy settings as wanted.
Troubleshooting Set up Errors
Set up points can stem from numerous components, together with incompatibility with current software program, inadequate disk house, or corrupted set up recordsdata. Fastidiously evaluate system necessities and guarantee sufficient cupboard space is out there. If errors persist, consult with the distribution’s devoted assist boards or documentation for tailor-made options.
Frequent Obtain and Set up Errors
| Downside | Doable Trigger | Resolution |
|---|---|---|
| Obtain interrupted | Community connectivity issues, server overload, short-term file points. | Test web connection. Retry obtain. If downside persists, contact assist or strive a distinct obtain mirror. |
| Set up fails | Inadequate disk house, corrupted set up recordsdata, conflicting software program. | Unlock disk house. Confirm obtain integrity (checksums). Test for and resolve software program conflicts. |
| Lacking dependencies | Required libraries or packages are absent. | Set up lacking dependencies utilizing package deal supervisor (e.g., apt, yum, pacman). |
| System incompatibility | {Hardware} or software program configuration conflicts. | Confirm system necessities and guarantee compatibility. Replace drivers or reinstall software program. |
Verifying Obtain Integrity
The integrity of downloaded recordsdata is paramount to keep away from corrupted installations. Make the most of checksums (MD5, SHA-256) to check the downloaded file’s hash in opposition to the official hash offered by the distribution. This ensures that the file hasn’t been tampered with throughout switch.
Troubleshooting Set up Points
A structured strategy is important when tackling set up issues. First, evaluate the set up logs for clues. Second, seek the advice of the distribution’s documentation or on-line boards. Third, take into account reverting to a earlier system state or beginning a recent set up.
Safety Issues
Safety ought to be a high precedence throughout the obtain and set up course of. Obtain from official sources to keep away from malicious recordsdata. Use robust passwords, and allow two-factor authentication the place accessible. Hold your system up to date with the most recent safety patches.
Instance: Corrupted Obtain
If a obtain fails partway via, the ensuing file is perhaps corrupted. A checksum mismatch will reveal this challenge. Obtain the file once more from a trusted supply and confirm the integrity utilizing the offered checksum.
Safety Issues: Os Unix Obtain
Defending your Unix-like system is paramount. A safe system safeguards your information and prevents unauthorized entry, guaranteeing a easy and productive expertise. A well-defended system is a resilient system.A sturdy safety posture begins with a eager consciousness of potential threats and a proactive strategy to mitigating them. Downloading and putting in a Unix distribution, whereas thrilling, ought to by no means be taken flippantly.
A diligent strategy to safety ensures that your new system is not only useful, but additionally fortified in opposition to potential threats.
Verifying Obtain Sources
Making certain the authenticity of your obtain supply is essential. Respected distribution websites are important. Search for digital signatures or checksums that verify the file hasn’t been tampered with. This helps stop malicious actors from injecting dangerous code into the installer. At all times obtain from official mirrors or trusted repositories.
Keep away from downloading from unverified or suspicious sources. Confirm the web site’s certificates and search for HTTPS within the tackle bar to make sure safe communication.
Sturdy Passwords and Account Administration
Creating robust passwords and managing accounts securely are basic safety practices. Keep away from simply guessable passwords like “password123”. Make use of a mixture of uppercase and lowercase letters, numbers, and symbols for optimum energy. Think about using a password supervisor for securely storing and producing advanced passwords. Frequently evaluate and replace your passwords to maintain them robust.
Implement multi-factor authentication wherever potential. Prohibit entry to delicate information and accounts.
Frequent Safety Vulnerabilities
Realizing potential vulnerabilities helps stop exploitation. Outdated software program is a major danger. Patching programs often is important to handle recognized safety flaws. Incorrect configuration also can go away your system uncovered. Make use of safe default settings and configurations each time potential.
Unauthorized entry makes an attempt are widespread. Sturdy firewall configurations and intrusion detection programs are very important for defending in opposition to these assaults. Denial-of-service assaults can disrupt your system. Configure your system to mitigate these assaults by limiting entry to sources.
Defending Towards Malware and Viruses
Common safety updates and the usage of antivirus software program are important for stopping malware infections. A sturdy antivirus program is essential for detecting and neutralizing malicious software program. Be cautious about opening attachments or clicking hyperlinks from unknown sources. Keep away from downloading and putting in software program from untrusted sources. Keep common backups of your information to safeguard in opposition to information loss as a consequence of malware or different points.
This supplies an important restoration mechanism.
Securing the Set up Course of
Securing the set up course of includes a number of essential steps. Set up the working system on a devoted partition to isolate it from different information. Use robust administrator passwords and restrict entry to administrator privileges. Disabling pointless providers reduces potential assault surfaces. Use a safe boot course of to stop malicious code from loading throughout system startup.
Confirm the integrity of the set up course of utilizing checksums or different verification strategies to ensure a clear set up.
Key Safety Suggestions
A safe Unix-like system requires proactive measures all through all the lifecycle, from obtain to set up. Prioritize safe obtain sources, sturdy passwords, and vigilant account administration. Frequently replace software program, preserve a powerful firewall, and make use of antivirus safety. These measures are important for a secure and resilient system.
